Leading on-line security that is easy, affordable, and does more to protect your people, assets, intellectual property, and organization from emerging threats.
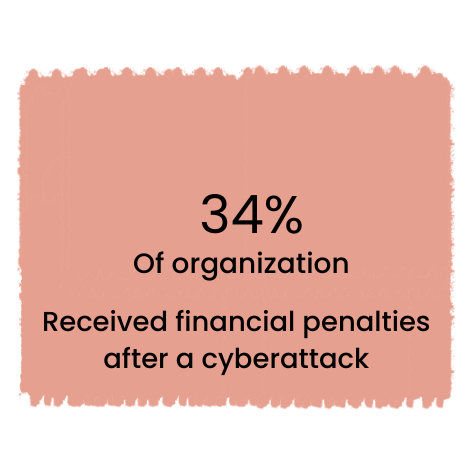
A financial consequence millions of dollars can result from a major cyberattack.
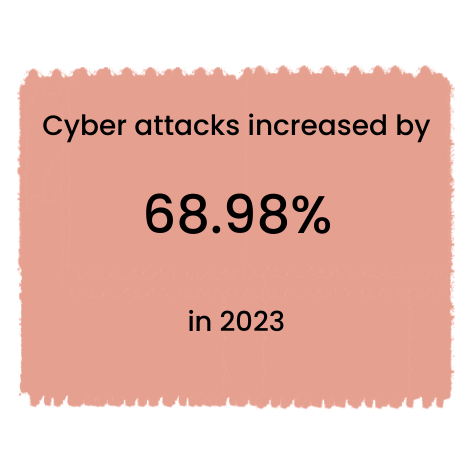
Cyber crimes increased from 11,523 cases in 2022 to 19,472 incidents in 2023.

Secure your business from the major threats simply and effectively with bedoo cyber security tools and services.
Proven security against these threats
Leading on-line security that is easy, affordable, and does more to protect your people, assets, intellectual property, and organization from emerging threats.
A financial consequence millions of dollars can result from a major cyberattack.
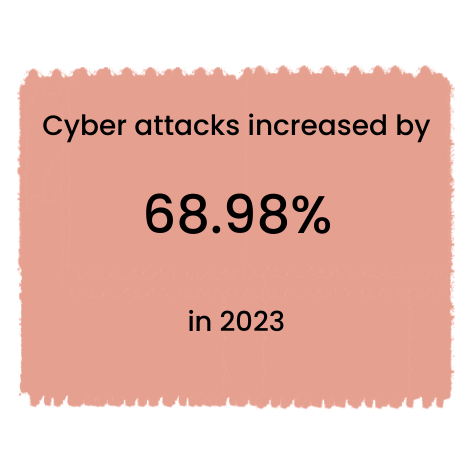
Cyber crimes increased from 11,523 cases in 2022 to 19,472 incidents in 2023.

Secure your business from the major threats simply and effectively with bedoo cyber security tools and services.
Proven security against these threats

Upgrade to your Next Generation Firewall
Ensure your data, assets, and users are protected across all environments with our advanced security solutions. Enhance your network's performance and secure your data-rich traffic and cloud-based applications. Stay ahead of cyber threats with consistent, real-time protection that shields you from new and sophisticated risks, minimizing potential security breaches.
Elevated Firewall protection
and security
and security
Unify organization’s security strategy regardless of where users and assets are physically located
Protect your company
reputation and reduce cost
reputation and reduce cost
Avoids paying regulatory fines, reputation and damages
Automated endpoint
protection
protection
Reduces network complexity and automates security posture across all edges

Monitors Network Traffic
Stop Virus Attack
Prevents Hacking
Stop Spyware
Promotes Privacy
Keeping Data Secured
Intelligent Port Control
Simple infrastructure
Updated Threat Protection
Consistent Network Speed
Comprehensive security for any threat

Upgrade to your Next Generation Firewall
Ensure your data, assets, and users are protected across all environments with our advanced security solutions. Enhance your network's performance and secure your data-rich traffic and cloud-based applications. Stay ahead of cyber threats with consistent, real-time protection that shields you from new and sophisticated risks, minimizing potential security breaches.
Elevated Firewall protection
and security
and security
Unify organization’s security strategy regardless of where users and assets are physically located
Protect your company
reputation and reduce cost
reputation and reduce cost
Avoids paying regulatory fines, reputation and damages
Automated endpoint
protection
protection
Reduces network complexity and automates security posture across all edges

Monitors Network Traffic
Stop Virus Attack
Prevents Hacking
Stop Spyware
Promotes Privacy
Keeping Data Secured
Intelligent Port Control
Simple infrastructure
Updated Threat Protection
Consistent Network Speed
Comprehensive security for any threat

We ensure that every user and device accessing your corporate applications and data is continuously verified, so you can trust that your security is always up to date and protected against unauthorized access.
Bringing zero trust principles to application access
Benefits
Unify organization’s security strategy regardless of where users and assets are physically located
Enable users to work from anywhere without disrupting operations
Helping prevent cyberthreats from
spreading laterally throughout
organizations

We ensure that every user and device accessing your corporate applications and data is continuously verified, so you can trust that your security is always up to date and protected against unauthorized access.
Bringing zero trust principles to application access
Benefits
Unify organization’s security strategy regardless of where users and assets are physically located
Enable users to work from anywhere without disrupting operations
Helping prevent cyberthreats from
spreading laterally throughout
organizations
Streamline network protection to a single
central service
Our UTM solution integrates multiple security features into one device, giving your network enhanced protection. Centralize your IT security for streamlined and efficient network defense.
Protect your business with the UTM combination
UTM for flexibility, cost-effectivity, and faster security solutions.
Starts at PHP3,685 monthly only
Streamline network protection to a single
central service
Our UTM solution integrates multiple security features into one device, giving your network enhanced protection. Centralize your IT security for streamlined and efficient network defense.
Protect your business with the UTM combination
UTM for flexibility, cost-effectivity, and faster security solutions.
Starts at PHP3,685 monthly only
Government

Hospitality

Manufacturing
Government

Hospitality

Manufacturing
What we do
Unbreakable Internet Managed IT Support Network Security Future Workspace IT Infrastructure CCTV
Connect with us!
Viber/Whatsapp
+63 956-458-6793 / 998.995.3139
Email
inquiry@bedoo.com.ph
What we do
Unbreakable Internet Managed IT Support Network Security Future Workspace IT Infrastructure CCTV
Connect with us!
Viber/Whatsapp
+63 956-458-6793 / 998.995.3139
Email
inquiry@bedoo.com.ph
